As healthcare organizations continue to evolve digitally, one thing has become clear – patient welfare cannot come first if the digital systems supporting it are under threat. According to the Journal of the American Medical Association (JAMA), the frequency of cyberattacks on hospitals and health systems more than doubled from 2016 to 2021.
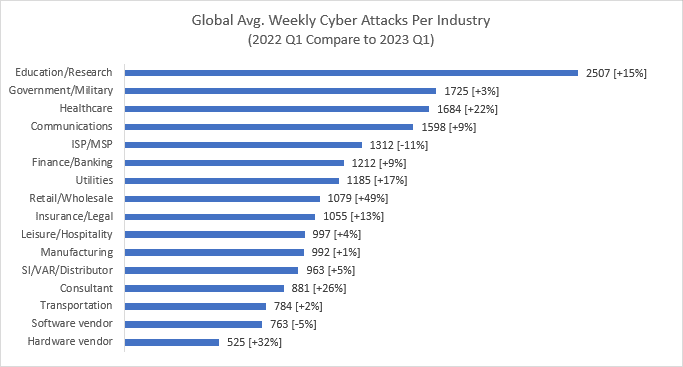
Research from Check Point Software Technologies confirms this trend, revealing that the healthcare sector experienced an average of 1,684 attacks per week in Q1 2023 – a year-on-year increase of 22%. That makes healthcare the third most targeted industry in 2023, ahead of finance, insurance, and communications.
These statistics are alarming, but they can be explained. The healthcare sector is a veritable goldmine of data, and much of it is managed through legacy IT systems that can be easily exploited. One survey by the Healthcare Information and Management Systems Society (HIMSS) found that 73% of healthcare provider organizations use legacy IT systems, which are costly to support and often rife with gaps in security.
This makes the sector an easy – and potentially lucrative – target for ransomware operators. But this vulnerability is not solely down to software and systems – it’s also down to how data and devices are managed within individual organizations.
The principle of “Zero Trust”
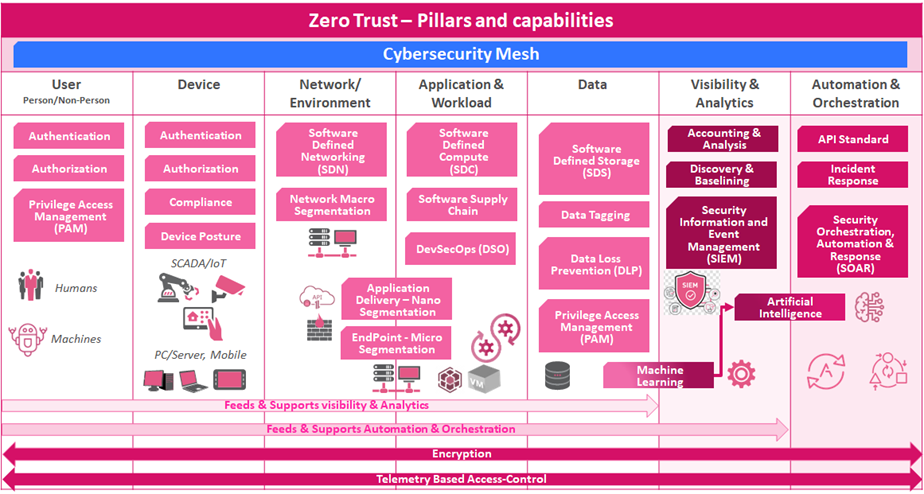
There is a division of responsibility when it comes to cyber resilience in sectors like healthcare. On the one hand, we have security enforcement and on the other, we have network control and policies. This is best reflected in the “seven pillars of zero trust” as defined by the Forrester and National Institute of Standards and Technology (NIST) frameworks.
Zero trust is a security model that operates on the principle of “never trust, always verify.” This means that access to resources and data should never be assumed to be safe, even if it is within the network perimeter.
The first five pillars are users, devices, networks, workloads, and data. These pillars make up the enforcement element of the framework, enforcing the “least privilege” principle by requiring ongoing identity and verification checks. The other two pillars are visibility and analytics, and automation and orchestration – these pillars make up the control and policies element of the framework, enhancing an organization’s security posture through real-time monitoring and automated responses in the event of a security breach.
These pillars, when brought together, enable companies to create a zero-trust environment, and this is precisely what healthcare organizations need to implement to fend off the rising number of attacks.
Common mistakes in network monitoring
There are some common mistakes that many healthcare organizations make when it comes to monitoring their network for threats, but the zero-trust approach can help to rectify them.
Failure to adopt a prevent-first approach
Just as it is better to inoculate a patient with a vaccine to prevent them from getting infected, it’s better to detect and prevent cyberattacks before they reveal themselves on a network. Real-time threat detection solutions can help to uncover anomalous traffic patterns, and real-time threat intelligence can actively block malware before it breaches a network.
Flat networks, or lack of segmentation
As healthcare organizations continue to digitize their services, their network footprint is growing. Vulnerable devices (endpoints) now extend to homes and other offices instead of a single site, so it’s important to “segment” or separate the network into more manageable clusters using firewalls and device-level protection. Just as a hospital might place fire doors around its building to prevent the spread of fire, a network should have barriers in place to prevent the lateral spread of any malware.
Not guarding end-point devices
An average 500-bed hospital might have as many as 10,000 connected Internet-of-Things (IoT) devices for monitoring, storing, and relaying patient information and other sensitive data. Enforcing a zero-trust policy will start with the “discovery” of these devices on the network, and will then automatically apply the least privilege, zero-trust policy so that only relevant systems or those who require access to carry out their duty will be able to access the devices.
Deploying outdated security controls
For security controls to be effective, they need to keep up with the pace of innovation. Retroactively deploying security controls to existing applications means that security is always one step behind innovation. To close the gap and ensure continuous security, security code should be integrated into the application development process as early as possible.
Using zero trust to strengthen healthcare networks
The implementation of Zero Trust principles is essential for healthcare organizations to ensure the security of patient data and critical infrastructure. Network monitoring is a subset of zero-trust visibility and analytics and is essential when it comes to identifying and categorizing information and understanding the flow of data.
Workloads refer to any application or service that operates in private data centers or public clouds, and this is where the principle of least privilege or “never trust, always verify” needs to be enforced. Healthcare organizations can strengthen their application workloads with zero trust by implementing continuous verification of identities and implementing preventive real-time security operations. Zero trust can be implemented in any application on-premises or in the cloud, depending on the security needs of the organization. A central hospital, for instance, might have different needs to a nursing home or home-care provider, where employees roam with devices or devices based in a range of locations.
Data must also be classified to be protected in the right way. For instance, securing unstructured data such as text, photos, video, and audio, and remote surgery with robotic systems like “Da Vinci” will all require varying degrees of protection and controls.
The pillars of zero trust can be deployed and implemented in a variety of ways to secure data pathways and automate threat responses, but the underlying goal remains the same – never trust, always verify. This is a “cyberculture” that healthcare organizations need to adopt if they are to weather the incoming storm.
